Welcome to the final article in the series of the Azure Governance blog posts. In this edition we will cover off compliance and the tools you can use to ensure your organisation's requirements are met.
This blog will approach the notion of Governance a little differently. By that we mean, the solutions from here on in will assume you’ve built out your environment. Now the question remains, how do I manage it, to meet my compliance objectives?
If you’ve missed the previous blogs, you can find them here - Part 1, Part 2 and Part 3. We would suggest reading these blogs to help put this last blog into context.
Where to now?
Now that you have a shiny new (cutting edge) environment, you’ve bedded down your governance framework, you’ve deployed agile solutions using automation, where to from here?
It goes without saying, but your Azure environment is not the sole responsibility of Microsoft, even though they take care of most of the heavy lifting. It really is a partnership where you ensure your own housekeeping. So, how do you manage it?
Azure Security Centre (ASC)
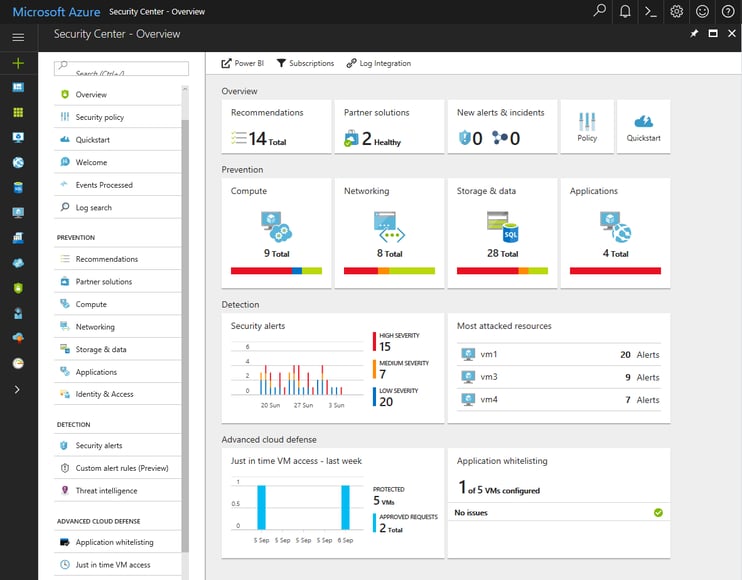
ASC is great for monitoring your environment(s) and assets against security. It provides centralised management of security components and threat detection so that you have a single pane of glass to work with.
Approximately one year ago, Microsoft announced the extension of Azure Security Centre into a hybrid model. This gives you the ability to extend monitoring to your on-premise environment, or environments running in other clouds. Microsoft have a detailed article that walks you through setting up monitoring, for non-Azure computers.
As you can see, it alleviates any concerns around complexity when you have multiple environments to manage by unifying security management. It also provides a great cost benefit.
The screenshot below details what ASC provides:
Why Azure Security Centre?
Here’s an article that details how you could detect such activities in your environment using ASC and it’s this example that solidifies why you should be taking advantage of this tool.
With that said, the ASC goes far beyond these capabilities. It also delivers the following added benefits:
- Centrally manage security policies across all your workloads to ensure compliance
- Proactively discover security threats across all your resources
- Act on security recommendations quickly and easily
- It allows you to focus on the most critical threats first by prioritising alerts
- Collate security data from a variety of sources and pipe that data into Power BI for additional insights
Microsoft recently announced the general availability of adaptive application controls in ASC. Adaptive application controls allow you to define a set of applications that can run on configured groups of virtual machines, essentially whitelisting EXE’s, MSI’s and scripts. It also applies rules you define in an automated fashion, monitors for violations of those rules and allows you to edit previously applied application whitelisting policies.
When configuring a new application control policy in adaptive application controls, audit mode is the default you’d typically run this for a two to four-week period, depending on the size of your environment, number of apps etc. to first observe the overall behaviour of your applications, before blocking them on the target VM. Once you’ve validated the applications you want to whitelist, create your rules then switch to enforce mode through the ASC UI.
This feature is available in the standard pricing tier and is available to try for free, for the first 60 days.
Well, that’s it for our series of Azure Governance blogs. We hope you have found the information valuable and it has provided you with what you need when considering a move to Azure. If you have any questions or need any assistance with your move to the Cloud, feel free to drop Eddie El-leissy, our Azure Solution Architect an email, he’d be more than happy to help.


